Android security updates All you need to be aware of Security patches are frequently released for phones, and there are simple methods to stay current on your phone specifically. If you’re interested to know what’s new on Android then you’re in the right spot.
Google has announced the latest Android Security Bulletin and has released corrections on Pixel devices.
These are exploits as well as other security issues that impact Android in general. Problems related to OS, kernel patching and driver updates could not impact any specific device, but they have to be rectified within the Android base by the people who are responsible for the code of the operating system (you know, Google. The company has outlined the improvements it made this month.
Overview of Android Architecture
Android is an open-source, Linux-based platform developed for a range of forms and devices. The following diagram illustrates the key elements that comprise Android. Android platform.
The Linux Kernel
The base to the Android platform is the Linux kernel. For instance Android Runtime (ART) Android Runtime (ART) relies on the Linux kernel to provide the underlying functions like threading and lower-level management of memory.
The use of the Linux kernel permits Android to benefit from essential security features. It also permits manufacturers of devices to develop hardware drivers that work with a well-known kernel.
Hardware Abstraction Layer (HAL)
The layer of abstraction for hardware (HAL) offers standard interfaces that allow devices to communicate with hardware capabilities to the more advanced Java API framework. The HAL is comprised of several libraries, all that implements an interface for the specific kind of component in the hardware, for example, the camera module or Bluetooth module. When an API framework calls to access hardware on the device and the Android system will load the library module associated with the hardware component.
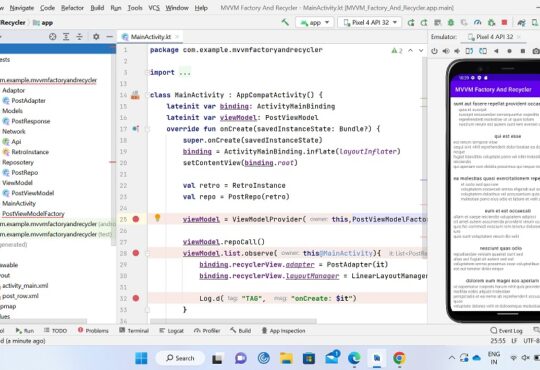
Android Runtime
For devices that run Android Version 5.0 (API Level 21) or greater every app runs within its own process , and has its own instance of Android Runtime (ART). The ART program is designed for multiple virtual machine running on memory-limited devices through the execution of DEX files, which is a specific bytecode format developed specifically for Android designed to have a minimal footprint on memory. Create toolchains, such as Jack and Jack, to and compile Java resources into DEX Bytecode that can be run in Android. Android platform.
Some of the most important characteristics of ART are as follows:
- ahead-of-time (AOT) as well as just-in-time (JIT) compilation
- Optimization of garbage removal (GC)
- With Android 9 (API level 28) and up, the conversion of app packages’ Dalvik Executable format (DEX) files to smaller machine code.
- Improved debugging capabilities, such as the dedicated sampling profiler, a detailed reports on diagnostic errors and crashes as well as the capability to create watchpoints that monitor certain areas.
In the past, prior to Android Version 5.0 (API Level 21), Dalvik was the Android runtime. If your application runs smoothly on ART, it will work with Dalvik also, but the opposite may not be the case.
Android also comes with the core runtime libraries that support the majority of the capabilities that are available in Java. Java programming language which includes the Java 8 language features which are part of the Java API framework makes use of.
Native C/C++ Libraries
Many of the key Android parts and functions, including ART and HAL are built using native code, which requires local libraries that are that are written using C as well as C++. The Android platform offers Java framework APIs that allow the functions native libraries to applications. For instance, you can use OpenGL ES through the Android framework’s Java OpenGL API to add the ability to draw and manipulate 3D and 2D images in your application.
If you’re creating an application that needs C or C++ code You can make use of an NDK for Android NDK to access some of the native library tools directly in your local code.
Java API Framework
The complete feature set included in Android OS is available to users via APIs that are written using the Java language. These APIs are the foundational blocks needed to build Android apps , by making it easier to simplify the reuse of core modular components and services of the system that include:
- A flexible and rich View System that you can utilize to design an application’s UI that includes grids, lists and text boxes, buttons and even an embeddable browser for web.
- A Resource Manager that provides access to non-code resources , such as localized strings, graphics and layout files
- A Notification Manager that allows every app to display custom notifications on the bar of status
- An Activity Manager oversees app lifecycles, and offers a common way to navigate back to the stack
- Content Providers allow apps to connect to data from other applications, like the Contacts app or communicate their own data
Developers can access the same framework APIs as Android applications that run on the system use.
System Apps
Android is a suite of apps that are essential for SMS, email and calendars, web browsing and contacts. Applications that come with Android do not have any special position among the apps the user decides to install. Thus, an app from a third party could become the user’s primary website browser or SMS messaging and even their default keyboard (some exceptions are made for the user’s Settings application).
The system apps work as apps for users as well as to provide essential capabilities that developers can access through their own application. For example, if the application would like to send text messages, you don’t have to create the functionality by yourself. You can instead use the SMS app that is installed and send messages to the user that you select.
Android Security Features
Here are the security features supplied by Android to help make the Android devices you design as secure as you can.
App sandbox
The Android platform makes use of the Linux user-based protection system to identify and block the resources of apps. In order to do that, Android assigns a unique user ID (UID) to every Android app , and then runs it as a separate procedure. Android makes use of this UID to establish the kernel-level App Sandbox.
App signing
App signing lets developers determine the source of the app as well as modify their apps without having to create complex interfaces and authorizations. Each app running in the Android platform has to have the app signed by its app’s developer.
Authentication
Android uses the concept of user-authentication-gated cryptographic keys that requires cryptographic key storage and service provider and user authenticators.
With devices that have fingerprint sensors the user can sign up one or more fingerprints , and make use of those fingerprints to unlock their device, as well as perform other functions. The Gatekeeper subsystem is responsible for the device pattern and password authentication within the Trusted Execution Environment (TEE).
Android 9 and higher includes protected Confirmation that lets users authentically confirm transactions that are important for example, like payment.
Biometrics
Android 9 and higher includes the BiometricPrompt API that app developers can make use of to incorporate biometric authentication into their applications in an open, device- and modeality-independent way. Only biometrics that are strong can be integrated in the BiometricPrompt.
Encryption
Once a device has been secured, all data that is created by users is encrypted automatically prior to placing it on disk, and all reads decrypt data prior to returning it to the process of calling. It also ensures that the uninitiated attempt get access to data they will not be able to access it.
Keystore
Android provides hardware-backed Keystore which allows for key generation as well as export and import of keys that are symmetric as well as import of raw symmetric keys encryption and decryption that is symmetric, with appropriate padding options and more.
Security-Enhanced Linux
To make up the Android security model, Android uses Security-Enhanced Linux (SELinux) to ensure the requirement for mandatory access control (MAC) over all processes, including processes which have superuser or root access rights (Linux capacities).
Trusty Trusted Execution Environment (TEE)
Trusty is a safe Operating System (OS) that offers the Trusted Execution Environment (TEE) for Android. The Trusty OS is run with the same processor as that of the Android OS, but Trusty is separated from the rest of the system through both software and hardware.
Verified Boot
Verified Boot is a method of ensuring that all executed code is from a reliable source (usually OEMs of devices) instead of an attacker or corrupt. It creates a complete chain of trust that starts from a secure root of trust , through the bootloader, and on to the boot partition as well as other partitions that are verified.
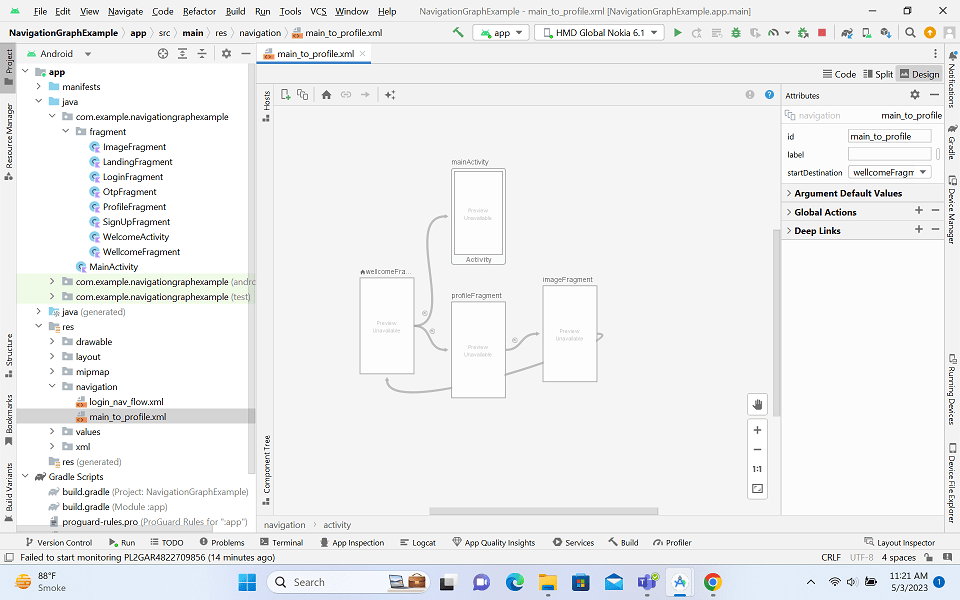
APK File Structure
The APK File is an archive that normally includes the following files as well as directories:
manifest File:An additional Android manifest file that explains the name of the application, its version access rights, as well as the references to library files used by the application. This file can be Android binary XML which can be transformed to human-readable plaintext XML by using tools such as AXMLPrinter2 and apktool. Androguard.
Signatures (META-INF):It contains the certificates as well as the signatures.
AssetsA Directory that contains assets of applications that can be searched via AssetManager.
Compiled resources(resources.arsc): A file containing precompiled resources, such as binary XML for example.
Native Libraries(lib):The directory with the compiled code is platform dependent. The directory is divided into several directories inside it:
ARMABIX-V7ACompilation of code for all ARMv7 and higher processors.arm64-v8ais compiled code that works with every ARMv8 arm64 and higher based processors.x86: compiled code that is intended for only x86 processorsx86_64Compilation of code only for x86 64 processors
Dalvik bytecode(class.dex):The classes that are written in the format dex files are is readable for Dalvik’s Dalvik virtual machine and Android Runtime. Android Runtime.
Resources(res): the directory that contains resources that are not integrated into resources.arsc
Read More:-
- Codeplayon Jetpack Compose Tutorial
- Codeplayon Android Tutorial
- Codeplayon Flutter Tutorial
- Codeplayon on Github