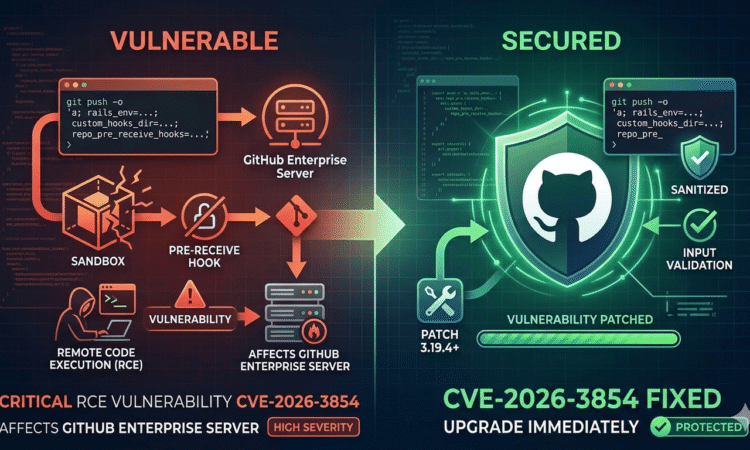
On March 4, 2026, Wiz Research reported a critical GitHub RCE vulnerability — tracked as CVE-2026-3854 with a CVSS score of 8.7 — that allowed any authenticated GitHub user to execute arbitrary commands on GitHub’s backend servers using a single git push command. No special tools. No privilege escalation. Just three semicolons and a standard git client.
GitHub validated and patched the flaw on GitHub.com in under two hours. But as of public disclosure, 88% of GitHub Enterprise Server (GHES) instances remained unpatched. Here is everything you need to know.
What Is the GitHub RCE Vulnerability CVE-2026-3854?
CVE-2026-3854 is classified as an improper neutralization of special elements (CWE-77) — a form of command injection — in how GitHub’s internal git push pipeline handled user-supplied input. The flaw resided in babeld, GitHub’s internal git proxy service, which processes every single push operation across the platform.
When a user runs git push -o key=value, they supply what are called push options — arbitrary strings that travel to the server alongside the push. The vulnerability existed because babeld embedded these strings verbatim into an internal semicolon-delimited header called X-Stat, without stripping or escaping the semicolon character. That one character is also the field delimiter in the X-Stat format.
The downstream service, gitrpcd, parsed the header using last-write-wins semantics — meaning a field appearing later in the header overrides any earlier occurrence of the same field. An attacker could therefore silently override server-set security fields simply by appending them to a push option value.
The result was a complete trust boundary failure between GitHub’s internal services — each of which assumed the data it received had already been validated by the component upstream.
Why the CVSS Score Understates the Real Risk
The official CVSS score of 8.7 is labeled “High” rather than “Critical” largely because exploitation requires authentication — the attacker must already have push access to at least one repository, including one they created themselves. But this framing is misleading. Any of the 150+ million GitHub users qualifies. Creating a free account and an empty repository takes under two minutes. In practical terms, the authentication requirement provided almost no meaningful barrier.
How the CVE-2026-3854 Exploit Chain Works — Step by Step.
The exploit is a three-step chain. Each step builds on the injected field from the previous one. Together they go from a harmless-looking git push to full, unsandboxed code execution on a GitHub backend server.
Step 1 — Inject a Non-Production rails_env Value to Bypass the Sandbox
The pre-receive hook binary inside GitHub Enterprise Server controls hook execution through the rails_env field it reads from the X-Stat header. When rails_env equals “production,” hooks run inside a sandbox.
Any other value disables the sandbox entirely and runs hooks directly as the git service user with full filesystem access. By injecting rails_env=staging (or any non-production string) at the end of a push option, an attacker flipped the server out of its secure execution path in a single field override.
Step 2 — Override custom_hooks_dir to Control the Hook Directory
With the sandbox disabled, the attacker’s next injection overrides the custom_hooks_dir field — the directory the pre-receive binary searches for hook scripts. By pointing this to an attacker-controlled location, the script lookup is redirected away from the legitimate hooks folder entirely.
Step 3 — Path Traversal via repo_pre_receive_hooks to Execute Any Binary
The final injection targets repo_pre_receive_hooks with a crafted path traversal payload. This causes the pre-receive binary to resolve and directly execute an arbitrary binary on the filesystem — running it as the git service user, with unsandboxed code execution and read/write access to the entire GHES instance, all hosted repositories, and internal service configuration.
The complete chain required no privilege escalation, no zero-day dependencies, and no tooling beyond a standard git client.
GitHub.com vs. GitHub Enterprise Server — Who Is Affected?
The impact on the two environments differs in one important technical detail.
On GitHub Enterprise Server, the custom hooks code path is active by default — making the exploit immediately usable once the sandbox is bypassed. On GitHub.com, that path is inactive by default because an enterprise_mode flag defaults to false.
However, this flag is also carried in the X-Stat header, making it equally injectable via the same mechanism. Wiz confirmed that once enterprise_mode was flipped via injection, code execution on GitHub.com was achievable on shared storage nodes — with read access to millions of public and private repositories belonging to entirely different users and organizations on that node.
This is the cross-tenant blast radius that makes the GitHub.com impact particularly severe despite the additional step.
GitHub’s CISO Alexis Wales stated in the official incident post that the forensic investigation was conclusive: every occurrence of the exploited code path in telemetry mapped exclusively to Wiz’s own testing. No customer data was accessed, modified, or exfiltrated.
Patched GHES Versions — Reference Table
GHES Branch | Vulnerable Status | Patched Version
—————————————————————–
GHES 3.14.x | Vulnerable (all prior) | 3.14.25 or later
GHES 3.15.x | Vulnerable (all prior) | 3.15.20 or later
GHES 3.16.x | Vulnerable (all prior) | 3.16.16 or later
GHES 3.17.x | Vulnerable (all prior) | 3.17.13 or later
GHES 3.18.x | Vulnerable (all prior) | 3.18.8 or later
GHES 3.19.x | Vulnerable (all prior) | 3.19.4 or later
GHES 3.20.0+ | Patched | 3.20.0 or later
How to Audit Your GHES Instance for Exploitation Attempts.
GitHub recommends reviewing your GHES audit logs for push operations that contain semicolons in push option values — the injection signature for this exploit. Run the following command on your GHES instance:
grep ';' /var/log/github-audit.log | grep 'push'
Any match should be treated as suspicious and investigated further. Identify the user account and repository associated with the push operation, review the full push option value, and determine whether any post-push activity on the server is unexplained. Even if you find nothing, document that you ran this check as part of your incident response record.
GitHub’s own investigation confirmed no exploitation in the wild. But given that GHES instances were potentially exposed for roughly seven weeks between the patch being available and public disclosure, this audit is a non-negotiable step.
How AI Discovered This GitHub RCE Vulnerability — A New Era for Security Research.
Most coverage of CVE-2026-3854 treats the AI discovery angle as a footnote. It deserves far more attention.
Wiz Research used AI-augmented reverse engineering tooling — specifically IDA MCP — to analyze GitHub’s closed-source compiled binaries and reconstruct the internal X-Stat protocol without access to the source code. The analysis that led to this critical CVE would have taken substantially longer through purely manual reverse engineering.
GitHub’s internal services are written in multiple languages, communicate through a shared internal protocol, and the compiled binaries that implement them are not publicly available.
This is, by most accounts, one of the first critical vulnerabilities in closed-source cloud infrastructure to be discovered primarily through AI-assisted binary analysis. The implications are significant. Closed-source software can no longer rely on opacity as even a partial security buffer.
Bug bounty hunters now have AI-powered tools capable of achieving the kind of cross-component protocol analysis that previously required rare, specialized expertise. Security teams maintaining proprietary infrastructure need to consider their own internal codebases through this new lens.
GitHub’s CISO confirmed this report will receive one of the highest rewards in the history of the GitHub Bug Bounty program — which has been running for over a decade. That reward level is consistent with the severity: a single authenticated user, any repository, full server access. AI-powered penetration testing tools in 2026 .
The Defense-in-Depth Lesson Every DevSecOps Team Should Take Away.
GitHub’s incident post makes a point that most news articles skipped entirely. The input sanitization fix is the primary remediation — but the exploit worked in part because a non-production code path was present in the production container image. It was never supposed to run there. It just happened to exist on disk.
GitHub has now removed that code path entirely from environments where it does not belong. The reasoning is important: even if a future injection vulnerability were discovered, removing the dead code path means there is nothing to pivot into. The blast radius is structurally smaller.
This is the defense-in-depth principle applied at the code deployment level — not just the network level. A few lessons worth internalizing for any team running microservice or containerized architectures:
• Audit container images for non-production code paths that shipped into production builds. Dead code in a prod image is an attack surface waiting for an injection vulnerability to activate it.
• Treat every field in a shared internal protocol as potentially attacker-controlled. If your architecture passes data between services through a delimiter-based format, ensure every service sanitizes input independently rather than trusting upstream components.
• The last-write-wins parsing pattern is a reusable vulnerability class. Any internal header, config file, or protocol that resolves duplicate keys by taking the last occurrence is a candidate for this type of injection if upstream input is ever embedded verbatim.
• Log push option values on your git infrastructure. This CVE demonstrated that user-supplied push metadata is a meaningful attack surface — treat it accordingly in your logging and alerting pipelines.
CVE-2026-3854 Disclosure Timeline
March 4, 2026 — ~09:00 UTC
Wiz Research discovers X-Stat injection vulnerability. Remote code execution confirmed on GHES 3.19.1.
March 4, 2026 — ~10:00 UTC
Wiz reports the vulnerability to GitHub via the Bug Bounty program. GitHub acknowledges receipt within the hour.
March 4, 2026 — 19:00 UTC
GitHub deploys a fix to GitHub.com. Forensic investigation launched; confirms no prior exploitation beyond researcher testing.
March 10, 2026
CVE-2026-3854 formally assigned with CVSS score of 8.7. GHES patches released across all supported version branches.
April 28, 2026
Public disclosure by Wiz and GitHub. Wiz telemetry indicates 88% of GHES instances remain unpatched at time of disclosure.
Frequently Asked Questions About CVE-2026-3854
Do I need to do anything if I use GitHub.com?
No. GitHub.com was patched on March 4, 2026 — the same day the vulnerability was reported. GitHub Enterprise Cloud and GitHub Enterprise Cloud with Data Residency were also patched that day. No action is required for users of these platforms.
What GitHub Enterprise Server versions are affected by CVE-2026-3854?
All GHES versions prior to 3.14.25, 3.15.20, 3.16.16, 3.17.13, 3.18.8, 3.19.4, and 3.20.0 are vulnerable. If you are running any GHES instance on a version older than the patched release in your branch, upgrade immediately.
Was any customer data stolen in the GitHub RCE vulnerability?
No. GitHub’s forensic investigation confirmed that every instance of the anomalous code path in its telemetry mapped exclusively to Wiz Research’s testing activity during vulnerability discovery. No customer data was accessed, modified, or exfiltrated.
What is a git push option and how was it used in this exploit?
Git push options are arbitrary key-value strings sent to the server via git push -o key=value. In CVE-2026-3854, GitHub’s babeld proxy embedded these values directly into an internal semicolon-delimited X-Stat header without stripping semicolons. Because the downstream parser used last-write-wins logic, attackers could inject extra fields by including a semicolon in their push option value — silently overriding security-critical server settings.
How did AI help discover the GitHub RCE vulnerability?
Wiz Research used a tool called IDA MCP for AI-augmented reverse engineering of GitHub’s closed-source compiled binaries. This enabled the team to reconstruct GitHub’s internal X-Stat protocol and identify the cross-component trust boundary flaw without access to source code — at a speed not feasible through manual analysis alone. It is considered one of the first critical CVEs in cloud infrastructure discovered this way.
Why are 88% of GitHub Enterprise Server instances still unpatched?
GitHub Enterprise Server is self-hosted, meaning organizations control their own patch schedules. Enterprise environments typically have longer change management cycles, mandatory testing periods, and maintenance windows — all of which delay patch deployment compared to cloud-hosted services. This gap is exactly why responsible disclosure timelines (seven weeks in this case) exist before public release.
What is last-write-wins header parsing?
Last-write-wins is a parsing behavior where, if a key appears multiple times in a structured header or configuration format, the final occurrence takes precedence and overrides all earlier values. In CVE-2026-3854, GitHub’s gitrpcd service parsed the X-Stat header this way. Because babeld embedded user input verbatim, attackers could append a duplicate security-critical field at the end of the header to override the legitimate server-assigned value.
CONCLUSION
CVE-2026-3854 is a sharp reminder that the attack surface of a platform is defined not just by its public API, but by every internal protocol it uses to move data between services. A single missing sanitization step in babeld, combined with a last-write-wins parser in gitrpcd and an unsandboxed dead code path in a production container, created one of the most exploitable critical vulnerabilities GitHub has ever faced.
If you run GitHub Enterprise Server, patch it today. If you manage any multi-service architecture that passes user-controlled data through shared internal protocols, audit it with this vulnerability class in mind. And if you run a bug bounty program, prepare for an era where AI-assisted binary analysis brings the security research community into your closed-source codebase faster than ever before.